- 開発技術
AWS Ingress Controllerのインストール
- #Kubernetes

目次
目的
【エンジニア募集中】フルリモート可◎、売上/従業員数9年連続UP、平均残業8時間、有給取得率90%、年休124日以上 etc. 詳細はこちらから>
Kubernetes(以下K8S)からAWSのApplication Load Balancerを利用するため
aws-load-balancer-controllerのアドオンをインストールします。
今回の記事は動作検証のため、EKSではなくEC2に構築したK8Sにインストールしています。
EKSにインストールする場合は、公式の手順をご確認願います。
AWS Load Balancer Controller アドオンのインストール – Amazon EKS
検証目的のため、本番運用では参考にしないようにお願いします。
前提
・AWS上にK8Sが構築済みであること
・kubectlコマンドが実行可能であること
EC2ロールにポリシーを追加します。
以下はAWSコンソールにログインして作業を行います。
①EC2のロールにインラインポリシーを追加します。
EC2に設定されているロール:dev-k8s-role※ここは自分のEC2に割り当てられているロールに置き換えてください。
②権限をjsonで指定します。
※必要な権限は以下から参照できます。以下はv2.4.4の権限となっています。
https://raw.githubusercontent.com/kubernetes-sigs/aws-load-balancer-controller/v2.4.4/docs/install/iam_policy.json
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 |
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "iam:CreateServiceLinkedRole" ], "Resource": "*", "Condition": { "StringEquals": { "iam:AWSServiceName": "elasticloadbalancing.amazonaws.com" } } }, { "Effect": "Allow", "Action": [ "ec2:DescribeAccountAttributes", "ec2:DescribeAddresses", "ec2:DescribeAvailabilityZones", "ec2:DescribeInternetGateways", "ec2:DescribeVpcs", "ec2:DescribeVpcPeeringConnections", "ec2:DescribeSubnets", "ec2:DescribeSecurityGroups", "ec2:DescribeInstances", "ec2:DescribeNetworkInterfaces", "ec2:DescribeTags", "ec2:GetCoipPoolUsage", "ec2:DescribeCoipPools", "elasticloadbalancing:DescribeLoadBalancers", "elasticloadbalancing:DescribeLoadBalancerAttributes", "elasticloadbalancing:DescribeListeners", "elasticloadbalancing:DescribeListenerCertificates", "elasticloadbalancing:DescribeSSLPolicies", "elasticloadbalancing:DescribeRules", "elasticloadbalancing:DescribeTargetGroups", "elasticloadbalancing:DescribeTargetGroupAttributes", "elasticloadbalancing:DescribeTargetHealth", "elasticloadbalancing:DescribeTags" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "cognito-idp:DescribeUserPoolClient", "acm:ListCertificates", "acm:DescribeCertificate", "iam:ListServerCertificates", "iam:GetServerCertificate", "waf-regional:GetWebACL", "waf-regional:GetWebACLForResource", "waf-regional:AssociateWebACL", "waf-regional:DisassociateWebACL", "wafv2:GetWebACL", "wafv2:GetWebACLForResource", "wafv2:AssociateWebACL", "wafv2:DisassociateWebACL", "shield:GetSubscriptionState", "shield:DescribeProtection", "shield:CreateProtection", "shield:DeleteProtection" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "ec2:AuthorizeSecurityGroupIngress", "ec2:RevokeSecurityGroupIngress" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "ec2:CreateSecurityGroup" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "ec2:CreateTags" ], "Resource": "arn:aws:ec2:*:*:security-group/*", "Condition": { "StringEquals": { "ec2:CreateAction": "CreateSecurityGroup" }, "Null": { "aws:RequestTag/elbv2.k8s.aws/cluster": "false" } } }, { "Effect": "Allow", "Action": [ "ec2:CreateTags", "ec2:DeleteTags" ], "Resource": "arn:aws:ec2:*:*:security-group/*", "Condition": { "Null": { "aws:RequestTag/elbv2.k8s.aws/cluster": "true", "aws:ResourceTag/elbv2.k8s.aws/cluster": "false" } } }, { "Effect": "Allow", "Action": [ "ec2:AuthorizeSecurityGroupIngress", "ec2:RevokeSecurityGroupIngress", "ec2:DeleteSecurityGroup" ], "Resource": "*", "Condition": { "Null": { "aws:ResourceTag/elbv2.k8s.aws/cluster": "false" } } }, { "Effect": "Allow", "Action": [ "elasticloadbalancing:CreateLoadBalancer", "elasticloadbalancing:CreateTargetGroup" ], "Resource": "*", "Condition": { "Null": { "aws:RequestTag/elbv2.k8s.aws/cluster": "false" } } }, { "Effect": "Allow", "Action": [ "elasticloadbalancing:CreateListener", "elasticloadbalancing:DeleteListener", "elasticloadbalancing:CreateRule", "elasticloadbalancing:DeleteRule" ], "Resource": "*" }, { "Effect": "Allow", "Action": [ "elasticloadbalancing:AddTags", "elasticloadbalancing:RemoveTags" ], "Resource": [ "arn:aws:elasticloadbalancing:*:*:targetgroup/*/*", "arn:aws:elasticloadbalancing:*:*:loadbalancer/net/*/*", "arn:aws:elasticloadbalancing:*:*:loadbalancer/app/*/*" ], "Condition": { "Null": { "aws:RequestTag/elbv2.k8s.aws/cluster": "true", "aws:ResourceTag/elbv2.k8s.aws/cluster": "false" } } }, { "Effect": "Allow", "Action": [ "elasticloadbalancing:AddTags", "elasticloadbalancing:RemoveTags" ], "Resource": [ "arn:aws:elasticloadbalancing:*:*:listener/net/*/*/*", "arn:aws:elasticloadbalancing:*:*:listener/app/*/*/*", "arn:aws:elasticloadbalancing:*:*:listener-rule/net/*/*/*", "arn:aws:elasticloadbalancing:*:*:listener-rule/app/*/*/*" ] }, { "Effect": "Allow", "Action": [ "elasticloadbalancing:ModifyLoadBalancerAttributes", "elasticloadbalancing:SetIpAddressType", "elasticloadbalancing:SetSecurityGroups", "elasticloadbalancing:SetSubnets", "elasticloadbalancing:DeleteLoadBalancer", "elasticloadbalancing:ModifyTargetGroup", "elasticloadbalancing:ModifyTargetGroupAttributes", "elasticloadbalancing:DeleteTargetGroup" ], "Resource": "*", "Condition": { "Null": { "aws:ResourceTag/elbv2.k8s.aws/cluster": "false" } } }, { "Effect": "Allow", "Action": [ "elasticloadbalancing:RegisterTargets", "elasticloadbalancing:DeregisterTargets" ], "Resource": "arn:aws:elasticloadbalancing:*:*:targetgroup/*/*" }, { "Effect": "Allow", "Action": [ "elasticloadbalancing:SetWebAcl", "elasticloadbalancing:ModifyListener", "elasticloadbalancing:AddListenerCertificates", "elasticloadbalancing:RemoveListenerCertificates", "elasticloadbalancing:ModifyRule" ], "Resource": "*" } ] } |
③ポリシーを作成します。
ポリシー名:dev-aws-load-balancer-controller
※ELBの部分に警告が表示されますが、無視で問題ありません。
公式の引用
注記
AWS Management Console でポリシーを表示すると、ELB の警告が表示されることがあります。
一部のアクションは ELB v2 にのみ存在するため、これらの警告は無視してもかまいません。ELB v2 の警告は表示されません。
K8Sノードが動作しているVPCサブネットにタグを追加します。
aws-load-balancer-controllerがサブネットを取得するためにタグが必要となります。
最低2つのサブネットにタグをつけて下さい。
K8Sクラスタ名:dev-k8s-cluster※ここは自分のK8Sクラスタ名に置き換えてください。
・privateサブネットの場合
【1】
キー:kubernetes.io/cluster/dev-k8s-cluster※クラスタ名は各自置き換えてください。
値:shared
【2】
キー:kubernetes.io/role/internal-elb
値:1
・publicサブネットの場合
【1】
キー:kubernetes.io/cluster/dev-k8s-cluster※クラスタ名は各自置き換えてください。
値:shared
【2】
キー:kubernetes.io/role/elb
値:※値は空白で構いません
今回はpublicサブネットのみなので、以下を設定しています。
K8SノードのspecにproviderIDを追加します。
以下はkubectlコマンドが実行可能な端末で作業を行います。
①K8SノードのspecにproviderIDを追加します。
今回はEKSを使用していないため、この作業が必要となります。
※EKSを使用している場合は自動で設定されるため不要な作業です。
providerIDを登録するため、事前に以下の情報が必要になります。
【A】:ノード名
【B】:ノードEC2のアベイラビリティゾーン
【C】:ノードEC2のインスタンスID
|
1 |
kubectl patch node 【A】 -p '{"spec":{"providerID":"aws:///【B】/【C】"}}' |
今回の検証機では以下となります。※ここは各自自分の環境に置き換えてください。
【A】:ip-172-31-33-167.ap-northeast-1.compute.internal
【B】ap-northeast-1d
【C】:i-0d281edb49d6bf046
|
1 |
kubectl patch node ip-172-31-33-167.ap-northeast-1.compute.internal -p '{"spec":{"providerID":"aws:///ap-northeast-1d/i-0d281edb49d6bf046"}}' |
aws-load-balancer-controllerのインストール
以下はkubectlコマンドが実行可能な端末で作業を行います。
①certmanagerのインストール
certmanagerのyamlファイルをダウンロードします。
|
1 |
curl -Lo cert-manager.yaml https://github.com/jetstack/cert-manager/releases/download/v1.5.4/cert-manager.yaml |
certmanagerをK8Sにインストールします。
|
1 |
kubectl apply -f cert-manager.yaml |
②aws-load-balancer-controller用crdsのインストール
aws-load-balancer-controller-crds.yamlファイルをkustomizeして作成します。
|
1 |
kubectl kustomize "github.com/aws/eks-charts/stable/aws-load-balancer-controller//crds?ref=master" > aws-load-balancer-controller-crds.yaml |
aws-load-balancer-controller-crdsをK8Sにインストールします。
|
1 |
kubectl apply -f aws-load-balancer-controller-crds.yaml |
③aws-load-balancer-controllerのインストール
aws-load-balancer-controllerのyamlファイルをダウンロードします。
|
1 |
curl -Lo v2_4_4_full.yaml https://github.com/kubernetes-sigs/aws-load-balancer-controller/releases/download/v2.4.4/v2_4_4_full.yaml |
※731行目の「your-cluster-name」となっているところを自分のK8Sクラスタ名に変更します。
K8Sクラスタ名:dev-k8s-cluster※ここは自分のK8Sクラスタ名に置き換えてください。
ファイル変更内容:v2_4_4_full.yaml
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 332 333 334 335 336 337 338 339 340 341 342 343 344 345 346 347 348 349 350 351 352 353 354 355 356 357 358 359 360 361 362 363 364 365 366 367 368 369 370 371 372 373 374 375 376 377 378 379 380 381 382 383 384 385 386 387 388 389 390 391 392 393 394 395 396 397 398 399 400 401 402 403 404 405 406 407 408 409 410 411 412 413 414 415 416 417 418 419 420 421 422 423 424 425 426 427 428 429 430 431 432 433 434 435 436 437 438 439 440 441 442 443 444 445 446 447 448 449 450 451 452 453 454 455 456 457 458 459 460 461 462 463 464 465 466 467 468 469 470 471 472 473 474 475 476 477 478 479 480 481 482 483 484 485 486 487 488 489 490 491 492 493 494 495 496 497 498 499 500 501 502 503 504 505 506 507 508 509 510 511 512 513 514 515 516 517 518 519 520 521 522 523 524 525 526 527 528 529 530 531 532 533 534 535 536 537 538 539 540 541 542 543 544 545 546 547 548 549 550 551 552 553 554 555 556 557 558 559 560 561 562 563 564 565 566 567 568 569 570 571 572 573 574 575 576 577 578 579 580 581 582 583 584 585 586 587 588 589 590 591 592 593 594 595 596 597 598 599 600 601 602 603 604 605 606 607 608 609 610 611 612 613 614 615 616 617 618 619 620 621 622 623 624 625 626 627 628 629 630 631 632 633 634 635 636 637 638 639 640 641 642 643 644 645 646 647 648 649 650 651 652 653 654 655 656 657 658 659 660 661 662 663 664 665 666 667 668 669 670 671 672 673 674 675 676 677 678 679 680 681 682 683 684 685 686 687 688 689 690 691 692 693 694 695 696 697 698 699 700 701 702 703 704 705 706 707 708 709 710 711 712 713 714 715 716 717 718 719 720 721 722 723 724 725 726 727 728 729 730 731 732 733 734 735 736 737 738 739 740 741 742 743 744 745 746 747 748 749 750 751 752 753 754 755 756 757 758 759 760 761 762 763 764 765 766 767 768 769 770 771 772 773 774 775 776 777 778 779 780 781 782 783 784 785 786 787 788 789 790 791 792 793 794 795 796 797 798 799 800 801 802 803 804 805 806 807 808 809 810 811 812 813 814 815 816 817 818 819 820 821 822 823 824 825 826 827 828 829 830 831 832 833 834 835 836 837 838 839 840 841 842 843 844 845 846 847 848 849 850 851 852 853 854 855 856 857 858 859 860 861 862 863 864 865 866 867 868 869 870 871 872 873 874 875 876 877 878 879 880 881 882 883 884 885 886 887 888 889 890 891 892 893 894 895 896 897 898 899 900 901 902 903 904 905 906 907 908 909 910 911 912 913 914 915 916 917 918 919 |
apiVersion: apiextensions.k8s.io/v1 kind: CustomResourceDefinition metadata: annotations: controller-gen.kubebuilder.io/version: v0.5.0 creationTimestamp: null labels: app.kubernetes.io/name: aws-load-balancer-controller name: ingressclassparams.elbv2.k8s.aws spec: group: elbv2.k8s.aws names: kind: IngressClassParams listKind: IngressClassParamsList plural: ingressclassparams singular: ingressclassparams scope: Cluster versions: - additionalPrinterColumns: - description: The Ingress Group name jsonPath: .spec.group.name name: GROUP-NAME type: string - description: The AWS Load Balancer scheme jsonPath: .spec.scheme name: SCHEME type: string - description: The AWS Load Balancer ipAddressType jsonPath: .spec.ipAddressType name: IP-ADDRESS-TYPE type: string - jsonPath: .metadata.creationTimestamp name: AGE type: date name: v1beta1 schema: openAPIV3Schema: description: IngressClassParams is the Schema for the IngressClassParams API properties: apiVersion: description: 'APIVersion defines the versioned schema of this representation of an object. Servers should convert recognized schemas to the latest internal value, and may reject unrecognized values. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#resources' type: string kind: description: 'Kind is a string value representing the REST resource this object represents. Servers may infer this from the endpoint the client submits requests to. Cannot be updated. In CamelCase. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#types-kinds' type: string metadata: type: object spec: description: IngressClassParamsSpec defines the desired state of IngressClassParams properties: group: description: Group defines the IngressGroup for all Ingresses that belong to IngressClass with this IngressClassParams. properties: name: description: Name is the name of IngressGroup. type: string required: - name type: object ipAddressType: description: IPAddressType defines the ip address type for all Ingresses that belong to IngressClass with this IngressClassParams. enum: - ipv4 - dualstack type: string loadBalancerAttributes: description: LoadBalancerAttributes define the custom attributes to LoadBalancers for all Ingress that that belong to IngressClass with this IngressClassParams. items: description: Attributes defines custom attributes on resources. properties: key: description: The key of the attribute. type: string value: description: The value of the attribute. type: string required: - key - value type: object type: array namespaceSelector: description: NamespaceSelector restrict the namespaces of Ingresses that are allowed to specify the IngressClass with this IngressClassParams. * if absent or present but empty, it selects all namespaces. properties: matchExpressions: description: matchExpressions is a list of label selector requirements. The requirements are ANDed. items: description: A label selector requirement is a selector that contains values, a key, and an operator that relates the key and values. properties: key: description: key is the label key that the selector applies to. type: string operator: description: operator represents a key's relationship to a set of values. Valid operators are In, NotIn, Exists and DoesNotExist. type: string values: description: values is an array of string values. If the operator is In or NotIn, the values array must be non-empty. If the operator is Exists or DoesNotExist, the values array must be empty. This array is replaced during a strategic merge patch. items: type: string type: array required: - key - operator type: object type: array matchLabels: additionalProperties: type: string description: matchLabels is a map of {key,value} pairs. A single {key,value} in the matchLabels map is equivalent to an element of matchExpressions, whose key field is "key", the operator is "In", and the values array contains only "value". The requirements are ANDed. type: object type: object scheme: description: Scheme defines the scheme for all Ingresses that belong to IngressClass with this IngressClassParams. enum: - internal - internet-facing type: string tags: description: Tags defines list of Tags on AWS resources provisioned for Ingresses that belong to IngressClass with this IngressClassParams. items: description: Tag defines a AWS Tag on resources. properties: key: description: The key of the tag. type: string value: description: The value of the tag. type: string required: - key - value type: object type: array type: object type: object served: true storage: true subresources: {} status: acceptedNames: kind: "" plural: "" conditions: [] storedVersions: [] --- apiVersion: apiextensions.k8s.io/v1 kind: CustomResourceDefinition metadata: annotations: controller-gen.kubebuilder.io/version: v0.5.0 creationTimestamp: null labels: app.kubernetes.io/name: aws-load-balancer-controller name: targetgroupbindings.elbv2.k8s.aws spec: group: elbv2.k8s.aws names: kind: TargetGroupBinding listKind: TargetGroupBindingList plural: targetgroupbindings singular: targetgroupbinding scope: Namespaced versions: - additionalPrinterColumns: - description: The Kubernetes Service's name jsonPath: .spec.serviceRef.name name: SERVICE-NAME type: string - description: The Kubernetes Service's port jsonPath: .spec.serviceRef.port name: SERVICE-PORT type: string - description: The AWS TargetGroup's TargetType jsonPath: .spec.targetType name: TARGET-TYPE type: string - description: The AWS TargetGroup's Amazon Resource Name jsonPath: .spec.targetGroupARN name: ARN priority: 1 type: string - jsonPath: .metadata.creationTimestamp name: AGE type: date name: v1alpha1 schema: openAPIV3Schema: description: TargetGroupBinding is the Schema for the TargetGroupBinding API properties: apiVersion: description: 'APIVersion defines the versioned schema of this representation of an object. Servers should convert recognized schemas to the latest internal value, and may reject unrecognized values. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#resources' type: string kind: description: 'Kind is a string value representing the REST resource this object represents. Servers may infer this from the endpoint the client submits requests to. Cannot be updated. In CamelCase. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#types-kinds' type: string metadata: type: object spec: description: TargetGroupBindingSpec defines the desired state of TargetGroupBinding properties: networking: description: networking provides the networking setup for ELBV2 LoadBalancer to access targets in TargetGroup. properties: ingress: description: List of ingress rules to allow ELBV2 LoadBalancer to access targets in TargetGroup. items: properties: from: description: List of peers which should be able to access the targets in TargetGroup. At least one NetworkingPeer should be specified. items: description: NetworkingPeer defines the source/destination peer for networking rules. properties: ipBlock: description: IPBlock defines an IPBlock peer. If specified, none of the other fields can be set. properties: cidr: description: CIDR is the network CIDR. Both IPV4 or IPV6 CIDR are accepted. type: string required: - cidr type: object securityGroup: description: SecurityGroup defines a SecurityGroup peer. If specified, none of the other fields can be set. properties: groupID: description: GroupID is the EC2 SecurityGroupID. type: string required: - groupID type: object type: object type: array ports: description: List of ports which should be made accessible on the targets in TargetGroup. If ports is empty or unspecified, it defaults to all ports with TCP. items: properties: port: anyOf: - type: integer - type: string description: The port which traffic must match. When NodePort endpoints(instance TargetType) is used, this must be a numerical port. When Port endpoints(ip TargetType) is used, this can be either numerical or named port on pods. if port is unspecified, it defaults to all ports. x-kubernetes-int-or-string: true protocol: description: The protocol which traffic must match. If protocol is unspecified, it defaults to TCP. enum: - TCP - UDP type: string type: object type: array required: - from - ports type: object type: array type: object serviceRef: description: serviceRef is a reference to a Kubernetes Service and ServicePort. properties: name: description: Name is the name of the Service. type: string port: anyOf: - type: integer - type: string description: Port is the port of the ServicePort. x-kubernetes-int-or-string: true required: - name - port type: object targetGroupARN: description: targetGroupARN is the Amazon Resource Name (ARN) for the TargetGroup. type: string targetType: description: targetType is the TargetType of TargetGroup. If unspecified, it will be automatically inferred. enum: - instance - ip type: string required: - serviceRef - targetGroupARN type: object status: description: TargetGroupBindingStatus defines the observed state of TargetGroupBinding properties: observedGeneration: description: The generation observed by the TargetGroupBinding controller. format: int64 type: integer type: object type: object served: true storage: false subresources: status: {} - additionalPrinterColumns: - description: The Kubernetes Service's name jsonPath: .spec.serviceRef.name name: SERVICE-NAME type: string - description: The Kubernetes Service's port jsonPath: .spec.serviceRef.port name: SERVICE-PORT type: string - description: The AWS TargetGroup's TargetType jsonPath: .spec.targetType name: TARGET-TYPE type: string - description: The AWS TargetGroup's Amazon Resource Name jsonPath: .spec.targetGroupARN name: ARN priority: 1 type: string - jsonPath: .metadata.creationTimestamp name: AGE type: date name: v1beta1 schema: openAPIV3Schema: description: TargetGroupBinding is the Schema for the TargetGroupBinding API properties: apiVersion: description: 'APIVersion defines the versioned schema of this representation of an object. Servers should convert recognized schemas to the latest internal value, and may reject unrecognized values. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#resources' type: string kind: description: 'Kind is a string value representing the REST resource this object represents. Servers may infer this from the endpoint the client submits requests to. Cannot be updated. In CamelCase. More info: https://git.k8s.io/community/contributors/devel/sig-architecture/api-conventions.md#types-kinds' type: string metadata: type: object spec: description: TargetGroupBindingSpec defines the desired state of TargetGroupBinding properties: ipAddressType: description: ipAddressType specifies whether the target group is of type IPv4 or IPv6. If unspecified, it will be automatically inferred. enum: - ipv4 - ipv6 type: string networking: description: networking defines the networking rules to allow ELBV2 LoadBalancer to access targets in TargetGroup. properties: ingress: description: List of ingress rules to allow ELBV2 LoadBalancer to access targets in TargetGroup. items: description: NetworkingIngressRule defines a particular set of traffic that is allowed to access TargetGroup's targets. properties: from: description: List of peers which should be able to access the targets in TargetGroup. At least one NetworkingPeer should be specified. items: description: NetworkingPeer defines the source/destination peer for networking rules. properties: ipBlock: description: IPBlock defines an IPBlock peer. If specified, none of the other fields can be set. properties: cidr: description: CIDR is the network CIDR. Both IPV4 or IPV6 CIDR are accepted. type: string required: - cidr type: object securityGroup: description: SecurityGroup defines a SecurityGroup peer. If specified, none of the other fields can be set. properties: groupID: description: GroupID is the EC2 SecurityGroupID. type: string required: - groupID type: object type: object type: array ports: description: List of ports which should be made accessible on the targets in TargetGroup. If ports is empty or unspecified, it defaults to all ports with TCP. items: description: NetworkingPort defines the port and protocol for networking rules. properties: port: anyOf: - type: integer - type: string description: The port which traffic must match. When NodePort endpoints(instance TargetType) is used, this must be a numerical port. When Port endpoints(ip TargetType) is used, this can be either numerical or named port on pods. if port is unspecified, it defaults to all ports. x-kubernetes-int-or-string: true protocol: description: The protocol which traffic must match. If protocol is unspecified, it defaults to TCP. enum: - TCP - UDP type: string type: object type: array required: - from - ports type: object type: array type: object nodeSelector: description: node selector for instance type target groups to only register certain nodes properties: matchExpressions: description: matchExpressions is a list of label selector requirements. The requirements are ANDed. items: description: A label selector requirement is a selector that contains values, a key, and an operator that relates the key and values. properties: key: description: key is the label key that the selector applies to. type: string operator: description: operator represents a key's relationship to a set of values. Valid operators are In, NotIn, Exists and DoesNotExist. type: string values: description: values is an array of string values. If the operator is In or NotIn, the values array must be non-empty. If the operator is Exists or DoesNotExist, the values array must be empty. This array is replaced during a strategic merge patch. items: type: string type: array required: - key - operator type: object type: array matchLabels: additionalProperties: type: string description: matchLabels is a map of {key,value} pairs. A single {key,value} in the matchLabels map is equivalent to an element of matchExpressions, whose key field is "key", the operator is "In", and the values array contains only "value". The requirements are ANDed. type: object type: object serviceRef: description: serviceRef is a reference to a Kubernetes Service and ServicePort. properties: name: description: Name is the name of the Service. type: string port: anyOf: - type: integer - type: string description: Port is the port of the ServicePort. x-kubernetes-int-or-string: true required: - name - port type: object targetGroupARN: description: targetGroupARN is the Amazon Resource Name (ARN) for the TargetGroup. minLength: 1 type: string targetType: description: targetType is the TargetType of TargetGroup. If unspecified, it will be automatically inferred. enum: - instance - ip type: string required: - serviceRef - targetGroupARN type: object status: description: TargetGroupBindingStatus defines the observed state of TargetGroupBinding properties: observedGeneration: description: The generation observed by the TargetGroupBinding controller. format: int64 type: integer type: object type: object served: true storage: true subresources: status: {} status: acceptedNames: kind: "" plural: "" conditions: [] storedVersions: [] --- apiVersion: v1 kind: ServiceAccount metadata: labels: app.kubernetes.io/component: controller app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-controller namespace: kube-system --- apiVersion: rbac.authorization.k8s.io/v1 kind: Role metadata: labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-controller-leader-election-role namespace: kube-system rules: - apiGroups: - "" resources: - configmaps verbs: - create - apiGroups: - "" resourceNames: - aws-load-balancer-controller-leader resources: - configmaps verbs: - get - update - patch --- apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRole metadata: creationTimestamp: null labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-controller-role rules: - apiGroups: - "" resources: - endpoints verbs: - get - list - watch - apiGroups: - "" resources: - events verbs: - create - patch - apiGroups: - "" resources: - namespaces verbs: - get - list - watch - apiGroups: - "" resources: - nodes verbs: - get - list - watch - apiGroups: - "" resources: - pods verbs: - get - list - watch - apiGroups: - "" resources: - pods/status verbs: - patch - update - apiGroups: - "" resources: - services verbs: - get - list - patch - update - watch - apiGroups: - "" resources: - services/status verbs: - patch - update - apiGroups: - discovery.k8s.io resources: - endpointslices verbs: - get - list - watch - apiGroups: - elbv2.k8s.aws resources: - ingressclassparams verbs: - get - list - watch - apiGroups: - elbv2.k8s.aws resources: - targetgroupbindings verbs: - create - delete - get - list - patch - update - watch - apiGroups: - elbv2.k8s.aws resources: - targetgroupbindings/status verbs: - patch - update - apiGroups: - extensions resources: - ingresses verbs: - get - list - patch - update - watch - apiGroups: - extensions resources: - ingresses/status verbs: - patch - update - apiGroups: - networking.k8s.io resources: - ingressclasses verbs: - get - list - watch - apiGroups: - networking.k8s.io resources: - ingresses verbs: - get - list - patch - update - watch - apiGroups: - networking.k8s.io resources: - ingresses/status verbs: - patch - update --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-controller-leader-election-rolebinding namespace: kube-system roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: aws-load-balancer-controller-leader-election-role subjects: - kind: ServiceAccount name: aws-load-balancer-controller namespace: kube-system --- apiVersion: rbac.authorization.k8s.io/v1 kind: ClusterRoleBinding metadata: labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-controller-rolebinding roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: aws-load-balancer-controller-role subjects: - kind: ServiceAccount name: aws-load-balancer-controller namespace: kube-system --- apiVersion: v1 kind: Service metadata: labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-webhook-service namespace: kube-system spec: ports: - port: 443 targetPort: 9443 selector: app.kubernetes.io/component: controller app.kubernetes.io/name: aws-load-balancer-controller --- apiVersion: apps/v1 kind: Deployment metadata: labels: app.kubernetes.io/component: controller app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-controller namespace: kube-system spec: replicas: 1 selector: matchLabels: app.kubernetes.io/component: controller app.kubernetes.io/name: aws-load-balancer-controller template: metadata: labels: app.kubernetes.io/component: controller app.kubernetes.io/name: aws-load-balancer-controller spec: containers: - args: - --cluster-name=dev-k8s-cluster # ★「your-cluster-name」を自分のK8Sクラスタ名に変更します。 - --ingress-class=alb image: amazon/aws-alb-ingress-controller:v2.4.4 livenessProbe: failureThreshold: 2 httpGet: path: /healthz port: 61779 scheme: HTTP initialDelaySeconds: 30 timeoutSeconds: 10 name: controller ports: - containerPort: 9443 name: webhook-server protocol: TCP resources: limits: cpu: 200m memory: 500Mi requests: cpu: 100m memory: 200Mi securityContext: allowPrivilegeEscalation: false readOnlyRootFilesystem: true runAsNonRoot: true volumeMounts: - mountPath: /tmp/k8s-webhook-server/serving-certs name: cert readOnly: true priorityClassName: system-cluster-critical securityContext: fsGroup: 1337 serviceAccountName: aws-load-balancer-controller terminationGracePeriodSeconds: 10 volumes: - name: cert secret: defaultMode: 420 secretName: aws-load-balancer-webhook-tls --- apiVersion: cert-manager.io/v1 kind: Certificate metadata: labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-serving-cert namespace: kube-system spec: dnsNames: - aws-load-balancer-webhook-service.kube-system.svc - aws-load-balancer-webhook-service.kube-system.svc.cluster.local issuerRef: kind: Issuer name: aws-load-balancer-selfsigned-issuer secretName: aws-load-balancer-webhook-tls --- apiVersion: cert-manager.io/v1 kind: Issuer metadata: labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-selfsigned-issuer namespace: kube-system spec: selfSigned: {} --- apiVersion: admissionregistration.k8s.io/v1 kind: MutatingWebhookConfiguration metadata: annotations: cert-manager.io/inject-ca-from: kube-system/aws-load-balancer-serving-cert labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-webhook webhooks: - admissionReviewVersions: - v1beta1 clientConfig: service: name: aws-load-balancer-webhook-service namespace: kube-system path: /mutate-v1-pod failurePolicy: Fail name: mpod.elbv2.k8s.aws namespaceSelector: matchExpressions: - key: elbv2.k8s.aws/pod-readiness-gate-inject operator: In values: - enabled objectSelector: matchExpressions: - key: app.kubernetes.io/name operator: NotIn values: - aws-load-balancer-controller rules: - apiGroups: - "" apiVersions: - v1 operations: - CREATE resources: - pods sideEffects: None - admissionReviewVersions: - v1beta1 clientConfig: service: name: aws-load-balancer-webhook-service namespace: kube-system path: /mutate-elbv2-k8s-aws-v1beta1-targetgroupbinding failurePolicy: Fail name: mtargetgroupbinding.elbv2.k8s.aws rules: - apiGroups: - elbv2.k8s.aws apiVersions: - v1beta1 operations: - CREATE - UPDATE resources: - targetgroupbindings sideEffects: None --- apiVersion: admissionregistration.k8s.io/v1 kind: ValidatingWebhookConfiguration metadata: annotations: cert-manager.io/inject-ca-from: kube-system/aws-load-balancer-serving-cert labels: app.kubernetes.io/name: aws-load-balancer-controller name: aws-load-balancer-webhook webhooks: - admissionReviewVersions: - v1beta1 clientConfig: service: name: aws-load-balancer-webhook-service namespace: kube-system path: /validate-elbv2-k8s-aws-v1beta1-targetgroupbinding failurePolicy: Fail name: vtargetgroupbinding.elbv2.k8s.aws rules: - apiGroups: - elbv2.k8s.aws apiVersions: - v1beta1 operations: - CREATE - UPDATE resources: - targetgroupbindings sideEffects: None - admissionReviewVersions: - v1beta1 clientConfig: service: name: aws-load-balancer-webhook-service namespace: kube-system path: /validate-networking-v1-ingress failurePolicy: Fail matchPolicy: Equivalent name: vingress.elbv2.k8s.aws rules: - apiGroups: - networking.k8s.io apiVersions: - v1 operations: - CREATE - UPDATE resources: - ingresses sideEffects: None --- apiVersion: networking.k8s.io/v1 kind: IngressClass metadata: labels: app.kubernetes.io/name: aws-load-balancer-controller name: alb spec: controller: ingress.k8s.aws/alb |
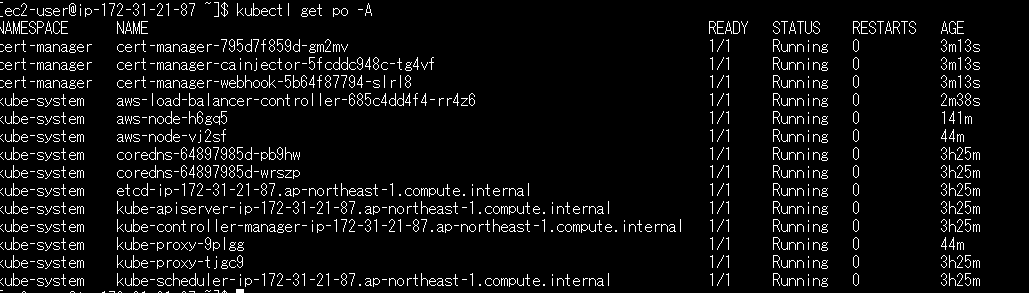
aws-load-balancer-controllerのSTATUSが「Running」になれば正常です。
サンプルnginxをデプロイします。
①nginxのyamlファイルを作成します。
作成ファイル:nginx.yaml
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
apiVersion: apps/v1 kind: Deployment metadata: name: nginx spec: selector: matchLabels: app: nginx replicas: 1 template: metadata: labels: app: nginx spec: containers: - name: nginx image: nginx:1.23.2 ports: - containerPort: 80 --- apiVersion: v1 kind: Service metadata: name: nginx spec: type: NodePort selector: app: nginx ports: - port: 80 |
②nginxをデプロイします。
|
1 |
kubectl apply -f nginx.yaml |
③nginxのデプロイを確認します。
ingress設定のデプロイ
①ingress.yamlファイルを作成します。
annotationsのgroup.nameは複数のポッドを一つのALBに纏めるときに使用します。
纏める必要がない場合、削除しても構いません
作成ファイル:ingress.yaml
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 |
apiVersion: apps/v1 kind: Deployment metadata: name: nginx spec: selector: matchLabels: app: nginx replicas: 1 template: metadata: labels: app: nginx spec: containers: - name: nginx image: nginx:1.23.2 ports: - containerPort: 80 --- apiVersion: v1 kind: Service metadata: name: nginx spec: type: NodePort selector: app: nginx ports: - port: 80 |
②ingress.yamlファイルをデプロイします。
|
1 |
kubectl apply -f ingress.yaml |
ingress設定を確認します。
以下はAWSコンソールで確認します。
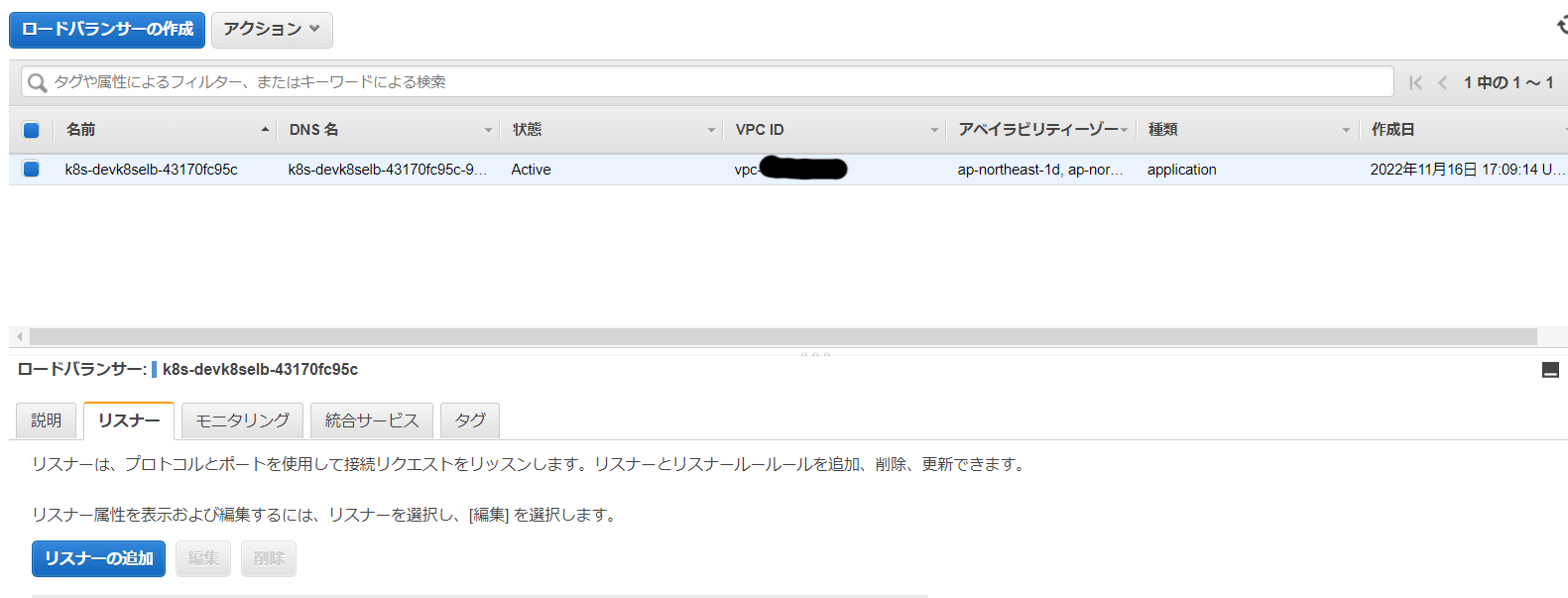
①Application Load Balancerが自動で作成されていることを確認します。
②Application Load Balancerのルールにnginxが設定されていることを確認します。
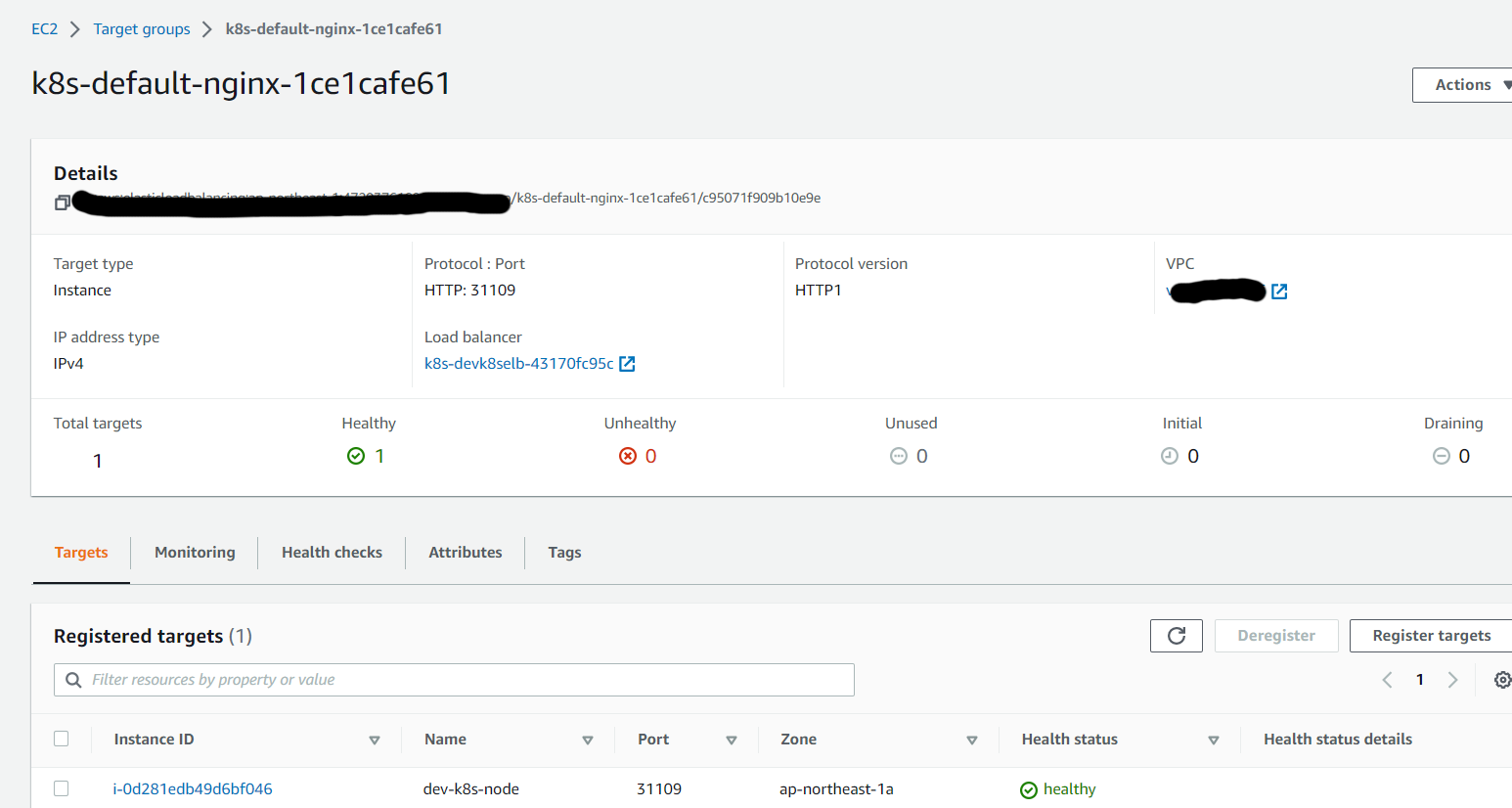
③target groupにK8SノードEC2が追加されていることを確認します。
④セキュリティグループにnginxのポートがアクセス許可されていることを確認します。
今回の場合ポート:31109が対象となります。
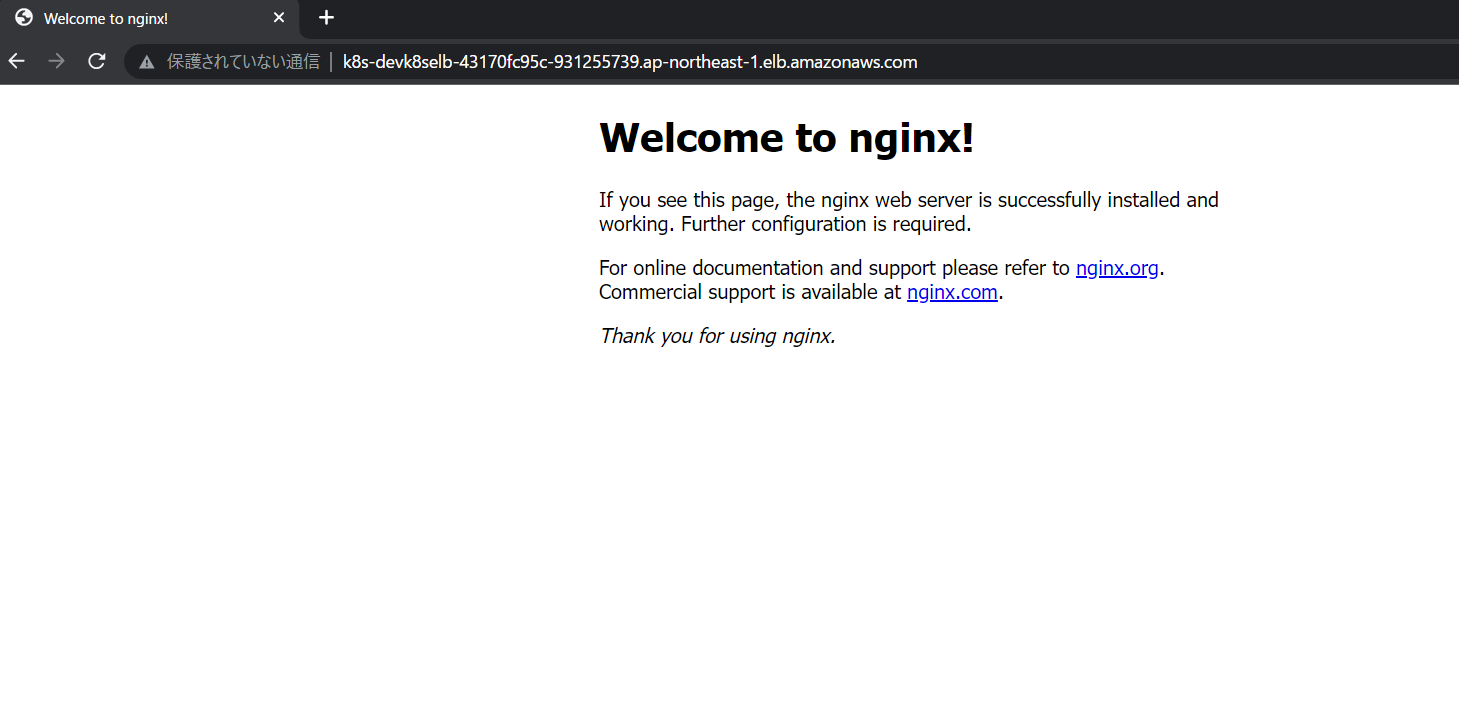
⑤ブラウザでApplication Load BalancerのDNSでアクセスします。
nginxのページが開けば正常です。
以上。
【エンジニア募集中】フルリモートも◎(リモート率85.7%)、平均残業8時間、年休124日以上、有給取得率90% etc. 詳細はこちらから>